Getting "pwned" is getting old.
Last month of so, I received another email telling me that some of my information has been discovered in a data breach of another website. This would normally alarm me, but I've gotten at least 8 in the past 2 years.

Photo by Markus Spiske / Unsplash
It is becoming too common to get an email from haveibeenpwned and this is not good. For those unaware this service allows users to sign up and then be alerted if that email has been compromised in a data breach.
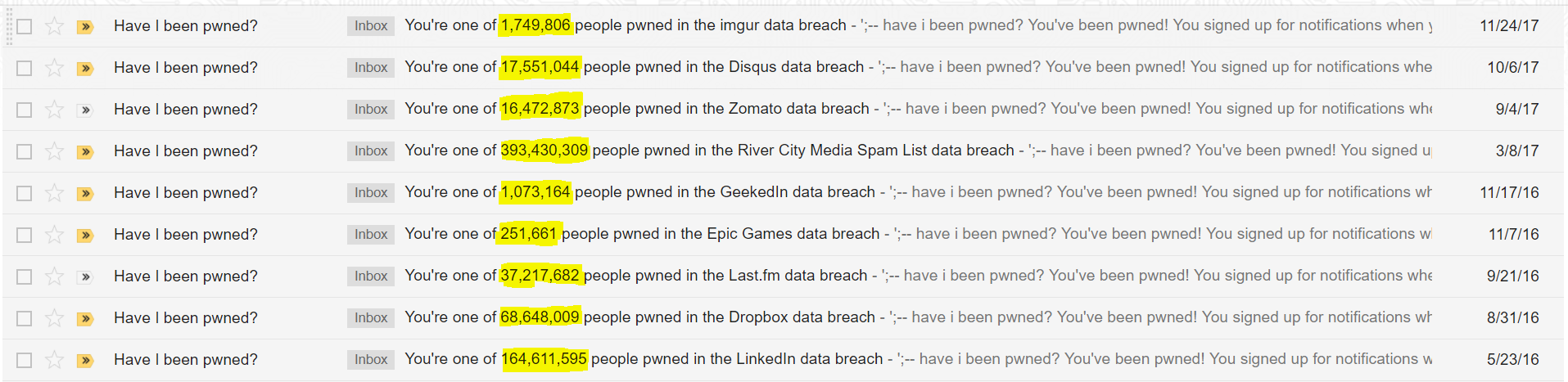
So taking a look at my email history we see an alarming number of affected users from even some large companies.
So what exactly was leaked? Taking a look at a random three data breaches I was involved in:
- Imgur
- Email addresses, Passwords
- GeekedIn
- Email addresses, Geographic locations, Names, Professional skills, Usernames, Years of professional experience
- River City Media Spam List
- Email addresses, IP addresses, Names, Physical addresses
First off, I have no idea what GeekedIn or River City Media Spam List is. I didn't voluntarily join either of those services. This article isn't about that but if you want to read about GeekedIn or River City the articles are linked. In short, some of these services harvested my information against my will, collected it, organized it and then lost it.
With this information out in the wild, there are plenty of situations where this data would come in handy. Talking over the phone to verify yourself might present some of the following questions:
- When is your birthday?
- Last 4 digits of Social?
- Name of street you live on?
These are what the industry is calling knowledge based authentication (KBA) and if you haven't noticed some of that information doesn't change (immutable). So after a data breach exposes that information, authentication methods have to evolve or they become quite easy to answer for an attacker.
With so many breaches the question most are asking is "Why does this site/service need this bit of information?" Which is a perfectly valid thing to ask. If I was a corporation my goal would be minimizing the data footprint I had by only asking for information my company needed to function. However, companies seem to be going in a different direction gobbling up as much of information they can gather under the disguise of analytics.
I don't want to live in a "box" scared to sign up on any website fearing my information being breached. However, as my personally involved breaches approaches double digits companies need to step it up before breaches start including information like fingerprints.